Enable SMB Signing On Microsoft Network Clients
If you have a Microsoft network client, you can configure it to digitally sign all of your network communications. This can be done in Group Policy, Security Settings, or Local Policies. Fortunately, the network client includes extensive “explain” text that explains how it works. However, you should read this article thoroughly before you start implementing it in your organization. Enable SMB Signing On Microsoft.
Microsoft SMB signing is an important security feature that protects against man-in-the-middle attacks. SMB signing works by placing a digital signature in each server message block. The digital signature is used by both clients and servers to ensure the authenticity of the contents of a message. It also prevents interlopers from stripping out the signature, so it is essential to enable SMB signing on client and server computers Google.
The new SMB signing security feature, Pre-Authentication Integrity, can prevent a malicious actor from interfering with the SMB connection. This security feature is available in Windows 10 and Windows Server 2016. It works by enabling cryptographic hashing to allow the client and server to trust the connection properties. In SMB 2.0 and earlier versions, this feature is disabled by default, but it can be enabled manually by the administrator.
How To Configuring SMB Signing:
Server Block Message (SMB) is the protocol for file and print communication. Without SMB signing, an attacker can intercept the message and take control of all share sessions on the network. This vulnerability is also found in older legacy networks that don’t support SMB signing.
SMB signing is a security feature that allows a network client to digitally sign all communication. This eliminates the risk of tampering and man-in-the-middle attacks. It is available on Windows Server 2003, Windows XP, and Windows NT 4.0. To enable SMB signing, configure your network client’s registry settings.
How To Man-In-The-Middle Attacks:
Configuring SMB signing for Microsoft requires changing a registry key called Require Security Signature. It is a good idea to restart Windows after making this change because otherwise it will not take effect. Make sure you reboot your Windows NT 4 workstation before you make the changes. If you don’t, it’s possible that you have misconfigured SMB signing on your network. Once you’ve configured it, you can use it to encrypt all communications.

SMB packet signing is necessary for many networking operations, including file and print sharing. It is a requirement of the SMB protocol. Without it, a Microsoft network client will not be able to communicate with an SMB server.
How To Changing The Status Of SMB Signing:
Changing the status of SMB signing in your Microsoft network server policy will allow you to configure whether your SMB server will negotiate packet signing with your clients. The recommended setting is Enabled. If you don’t want to enable SMB signing on your network server, you can change this setting to Disabled.
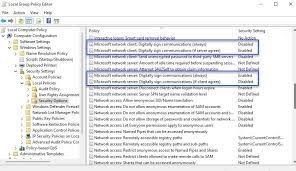
To enable SMB signing, you must enable it on both Windows systems. To enable SMB signing on Windows systems, go to Computer Configuration, Policies, Windows Settings, Security Settings, and Local Policies. There, you can enable or disable all the policy items. These items apply to systems that are running SMB server services and Windows systems that serve files and printers.
Select Start Settings:
- The SMB signing policy can be found under Computer
- Configuration > Windows Settings > Security Settings > Local Policies > Security Options.
SMB is a client-server protocol that uses NTLM or Kerberos protocols to authenticate users. To enable SMB on a Windows computer, you need to have both a Lanman Server and Lanman Workstation service installed. You can use the Get-Service Lanman* PowerShell command to determine which one of these services is active.

Leave a Reply