How to Enable Two-Factor Authentication
Enable 2fa (2FA) adds an extra layer of security to your account. It requires a code sent to your trusted phone number or a third-party security app to log in.
By enabling 2FA you’ll make it much harder for hackers to access your account, even if they know your password. Plus you’ll get a sweet Fortnight Boogie Down dance emote!
Enabling two-factor authentication (2FA) is a crucial step in securing your online accounts and adding an extra layer of protection beyond just a password. In this comprehensive guide, we will walk you through the process of enabling 2FA, explaining its importance, different methods, and offering tips for a secure setup.
1. Understanding Two-Factor Authentication (2FA)
Two-factor authentication is a security process that requires users to provide two different authentication factors to verify their identity. These factors typically fall into three categories: something you know (e.g., a password), something you have (e.g., a smartphone), and something you are (e.g., fingerprint or facial recognition).
2. Importance of 2FA
Enabling 2FA significantly enhances your account security. Even if a malicious actor obtains your password, they won’t be able to access your account without the second authentication factor. This adds an extra layer of defense against unauthorized access, protecting your sensitive information and personal data.
3. Choosing the Right 2FA Method
There are several methods for implementing 2FA, and the choice often depends on the service or platform you’re using. Common methods include:
- SMS Authentication: This method involves receiving a one-time code via text message to your registered mobile number.
- Authentication Apps: Apps like Google Authenticator or Authy generate time-sensitive codes that you enter during the login process.
- Email Authentication: A code is sent to your registered email address for verification.
- Hardware Tokens: Physical devices, such as security keys or smart cards, provide a second factor for authentication.
4. Enabling 2FA on Popular Platforms
Now, let’s look at how to enable 2FA on some commonly used platforms:
- Google/Gmail:
- Go to your Google Account settings.
- Navigate to “Security.”
- Select “2-Step Verification” and follow the setup process.
- Facebook:
- Access your Facebook Settings.
- Click on “Security and Login.”
- Enable “Two-Factor Authentication” and follow the instructions.
- Twitter:
- Go to Twitter Settings.
- Select “Account” and then “Security.”
- Enable “Login verification” to set up 2FA.
- Microsoft (Outlook, Hotmail):
- Access your Microsoft Account settings.
- Navigate to “Security.”
- Turn on “Two-step verification.”
5. Best Practices for Secure 2FA Setup
- Use App-Based 2FA: Authentication apps are generally more secure than SMS-based methods, as they are less susceptible to SIM card swapping attacks.
- Backup Codes: Save backup codes provided during setup in a secure location. These codes can be used if you lose access to your primary 2FA method.
- Recovery Options: Ensure you have a recovery email or phone number set up in case you ever need to regain access to your account.
- Regularly Review Security Settings: Periodically check your security settings and review the devices that have access to your accounts.
6. Troubleshooting and Tips
- Lost Access to 2FA Device:
- Each platform has specific account recovery processes. Follow the provided instructions if you lose access to your 2FA device.
- Security Key Consideration:
- If using a security key, make sure it is compatible with the platform you’re securing.
- Educate Yourself:
- Stay informed about the latest 2FA methods and security best practices.
By following these steps and best practices, you’ll significantly enhance the security of your online accounts. Remember, the extra time spent setting up 2FA is a small price to pay for the added protection it provides against potential security threats.
1. Enable 2fa
Enabling 2FA is the best way to keep your account secure. It requires someone who wants to access your account to not only know your password but also have access to your secondary method of authentication. This makes it much more difficult to hack an account, and if something does happen to your secondary device or you lose access to your primary method (like a phone number change), you can use backup codes to regain access.
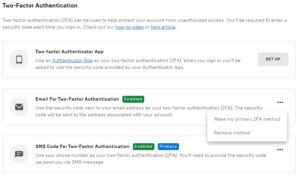
To enable 2FA on your account, log in to HubSpot and click the settings settings icon in the main navigation bar or burger menu icon in the left sidebar menu and navigate to Security. On the Trusted Phone Number or Third party security app screen, follow the setup instructions to set up your secondary method. A six-digit code will be sent to your secondary device or to the third-party security app. Input the code and click Verify.
Almost all major services now offer 2FA, from social media to online gaming. While it might take a little extra time to set up, doing so adds an additional layer of security that makes it significantly more difficult for hackers to get into your account. Plus, some services like Fortnite offer rewards for enabling 2FA, such as the Boogie Down emote, so it’s worth the extra step!
2. Set up a trusted phone number
When a person uses 2FA, they’re logging in with two things: their username/password and another way to verify their identity known as an authentication factor. The other method must be something the user knows (like their zip code) or has possession of (like a personal cell phone). Second factors can include anything from third-party authenticator apps to hardware security keys. But if hackers find the one or two things that make up the user’s authentication factor, they can access their accounts, devices and information.
SMS (2FA via text message) is one of the most popular ways to enable 2FA because of its simplicity and ease of use. However, it comes with a number of vulnerabilities. If a user loses their phone or changes their mobile number, they’re left vulnerable to hacking and data breaches.
Additionally, text messages can be intercepted during a Wi-Fi or cellular connection and can end up in the wrong hands. The other problem with SMS is that it only works on the device it’s sent to. If a user has multiple phones or is traveling abroad, they will be unable to log in.
For these reasons, it’s best to avoid using SMS 2FA when possible. Instead, try using a third-party authenticator app or a physical security key. Duo even offers self-remediation features that warn users or block their account if their devices aren’t meeting certain requirements, such as having up to date operating systems and secure wireless connections.
3. Set up a third-party security app
Two-factor authentication (2FA) helps prevent hackers from accessing an account or device with just the hacker’s knowledge of a password. This is because attackers need to have a second piece of information in order to log in, like a verification code sent via text or an authenticator app, or even something that only the user has, such as a physical security key.
As many popular social media platforms are notorious for account hacks and login shenanigans, enabling 2FA on these accounts can help make it harder to be hacked. Additionally, adding 2FA to other accounts, such as cloud storage services or financial platforms, can also improve security and reduce the risk of a data breach.
When a user logs into an account with 2FA enabled, they will be required to provide a 6 digit authentication code in addition to their general access credentials. This can be provided via a mobile authenticator app, SMS code, or backup codes that are generated by the system and saved within a user’s profile.
The ability for users to generate and save these backup codes can help mitigate some of the logistical challenges that come with rolling out 2FA. For example, if a user travels abroad, they may not be able to receive an SMS or mobile authenticator app notification on their smartphone due to the lack of cell coverage in that location. To combat this, some solutions like Duo allow users to approve access requests from their computer or laptop through push notifications that appear on the screen, reducing the likelihood of user approval of malicious activity.
4. Set up a physical security key
A physical security key is one of the most secure ways to enable 2fa. These devices plug into a USB port and provide a cryptographic signature when plugged in, verifying the identity of the user. Unlike SMS (which is vulnerable to SIM swap attacks) or apps that generate codes (which are susceptible to phishing), these keys are more difficult for attackers to obtain or fake.
To set up 2fa with a physical security key, users must first log into their account in a web browser and click on “Authentication steps” to add the device. When prompted, they will be asked to insert their security key and to enter a name for the device (to help distinguish them from other devices). They will then be able to use that security key to verify their logins in place of receiving a code via SMS or an app.
The security key must be compatible with FIDO2 (Fast IDentity Online). Most physical security keys support this standard, such as Yubico’s line of products. For more information on how to enable FIDO2 2fa with a specific service, please refer to that company’s documentation. In addition, users must be logged into their account on a device that supports FIDO2. This includes the device on which they want to add the security key as well as any Auth0 Applications they may have access to.
Leave a Reply